02.10.2023
Share
Digital transformation is a necessary action during a recession. It's not only an anti-crisis measure but also an anti-recession measure.
Read more02.10.2023
Share21.07.2022
Share09.06.2022
Share19.05.2022
Share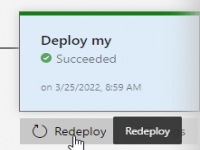
Increasing developer effectiveness gives you a competitive advantage and helps you meet SLA. In this blog post Janis Veinbergs will discuss how to improve the deployment process from the traditional file copy to something more effective, automated, and low friction while causing no downtime to end-users.
Read more24.09.2021
Share
The providers acting in the market offer different options of data storage: VPS and VDS (Virtual Private Server and Virtual Dedicated Server - the virtual private and allocated servers), dedicated servers, hosting or rent of disk space. The latter solution is considered the most budgetary and suitable for small web projects. However, hosts have not only advantages, but also a number of limitations that need to be remembered by choosing this way of storing data.
Read more02.09.2021
Share
Digitalization of business processes is a long-term investment in the stable future of the company. The introduction of new IT solutions will not help predict the next pandemic or other changes, but will make the company more flexible and adaptive to reality, which helps to effectively overcome the crisis.
Read more19.08.2021
Share
Problems in the field of ecology, one way or another, are relevant for all countries. These issues affect not only activists, but also business. Currently, there is a trend towards responsible investment. About 97% of investors, according to the audit and consulting company EY (UK), when deciding to cooperate with a particular company, are guided by its ESG index.
Read more09.07.2021
Share07.07.2021
Share
COVID-19 hit numerous industries, but the data centre market remained in favour. According to various studies, revenue for 2020 increased by a quarter. The massive transition to remote work and widespread self-isolation exacerbated information security issues, as well as revealed a new layer of users who were forced to encounter online space and were just beginning to digitalize their communication, entertainment, shopping and other vital aspects. In this regard, cyber defense issues will remain especially relevant in 2021. The trend is also facilitated by the tendency to maintain remote jobs during the post-pandemic recovery period.
Read more18.06.2021
Share
Efficiency of management and security of a data storage system (DSS) directly affect the performance of companies of different scales, ranging from start-ups to large corporations of federal outreach. The selection of a specific solution must be based on the tasks to be addressed, types of the information used by the entity (unstructured files, big data, DBMS, archives, back-up copies, media and many others), as well as the required information processing speed.
Read more Flexible service
Flexible service
Superfast and tailored solutions for specific and complex requirements.
 Fast customer support
Fast customer support
Choose the most convenient way to receive fast DEAC support 24/7.
 Experienced IT experts
Experienced IT experts
Professional and certified IT support 24/7.
